This post was originally published on this site.
Small businesses face a silent but looming danger. The password credentials to a growing number of apps vital to operations remain vulnerable.
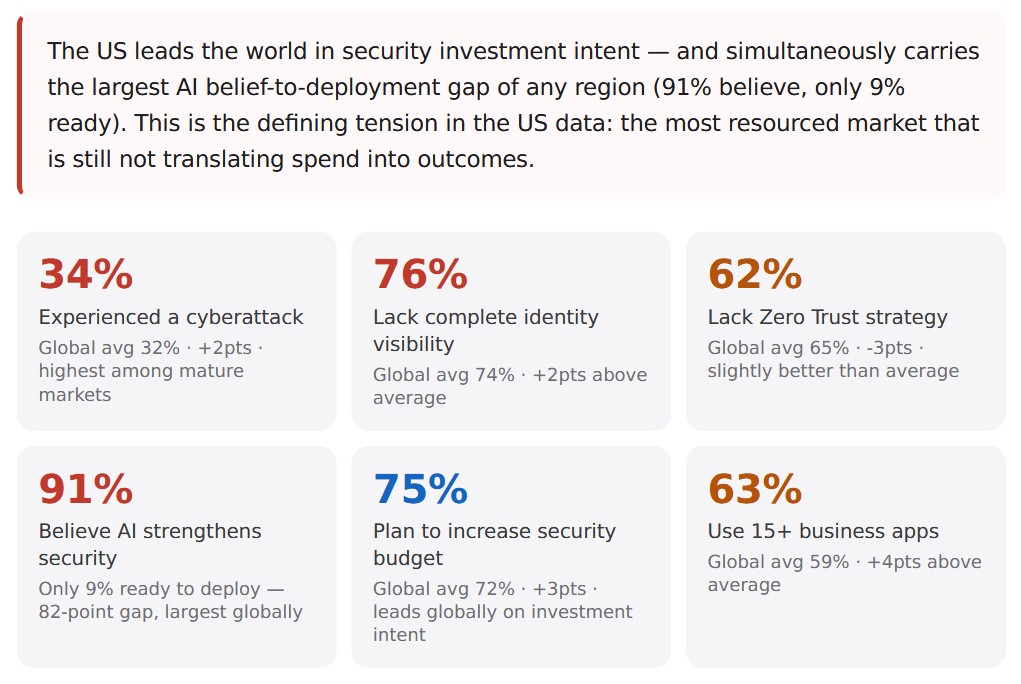
And U.S. businesses seem more at risk than their counterparts in other markets even though they spend more on security.
A recent survey conducted by Tigon Advisory Corp uses 3,322 responses worldwide from nine regions and six industries to better understand the level of threat.
Despite awareness of the problem however, a stunning number of companies have done little or nothing to address it.
“Workforce password security sits at a critical inflection point,” the report explains. “Organizations understand the risk in theory but have not converted that understanding into deployed security infrastructure.”
Fortunately, Zoho Corp., who commissioned the survey, offers a few solutions to consider when trying to avert the issue.
Contact the Zoho team today or read on for more about the threats your business faces.
U.S. Small Businesses Face Especially High Threat
You may operate a car rental business in Phoenix, Arizona or a lawn and garden business in Lynchburg, Virginia.
Though not specifically technology companies, either of these businesses may use software from digital booking apps to invoicing and client CRMs that make them vulnerable.
In fact, in either case, these businesses stand a better chance of being a victim of a cyber attack simply because they are based in the United States.
You read that right!
According to the Tigon survey, 34% of U.S. businesses reported being victims of a cybercrime last year compared to just 32% worldwide.
Application Sprawl Heightens Danger of Cyberattacks
A big reason for this vulnerability comes down to something called application sprawl.
You may run a chain of Cuban coffee shops in and around Miami, Florida. Or perhaps you founded a bike messenger service in New Orleans, Louisiana.
In either case, growing reliance on everything from payment portals to scheduling apps and digital task management software also elevates risk.
“As organizations grow more dependent on digital applications with most employees now accessing more than 15 business apps daily, credentials have become the most consistently exploited vulnerability in modern organizations,” the report adds.
The Disappearance of Single Logins Leads to More Security Challenges
Maybe you operate a vacation rental business in the Adirondacks in New York State. Or perhaps you manage a biotech company based in Salt Lake City, Utah.
In either case, the use of more and more applications and more hybrid or even remote work, means greater security challenges.
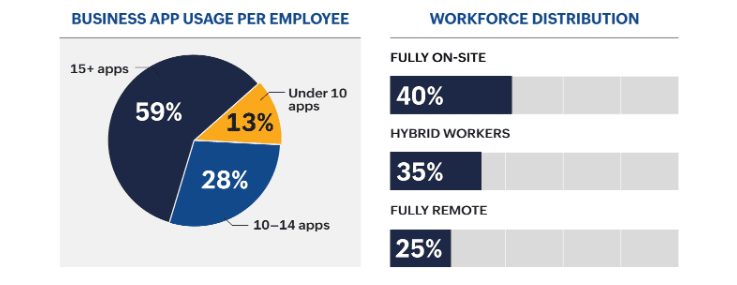
According to the survey, 63% of U.S. respondents say their employees use 15 or more apps daily, four points above the 59% global average.
These statistics again demonstrate how those operating a business in the U.S. face a greater threat than those doing so in other global markets.
Add to this the fact that only 40% of workers on average now work on site at businesses surveyed worldwide. Meanwhile, 35% of employees work hybrid while 25% now work fully remote.
“The modern workforce no longer operates from a single login,” the survey concludes. “Employees access a sprawling constellation of business applications. Each application represents a credential that must be created, secured, and governed, creating an attack surface that most organizations cannot fully see.”
Security Stacks Lack Future Readiness
Most businesses surveyed admit they are not ready for the security risks of the future.
Sure, 75% of U.S. businesses plan to increase their security budgets over the next five years. Only 72% of respondents worldwide plan to do so. But even this may not be sufficient.
Afterall, 80% of responding organizations worldwide say their software architecture lacks the capabilities to stand up to tomorrow’s threats – even with added budgets.
Risks Increase For Businesses With Smaller Teams
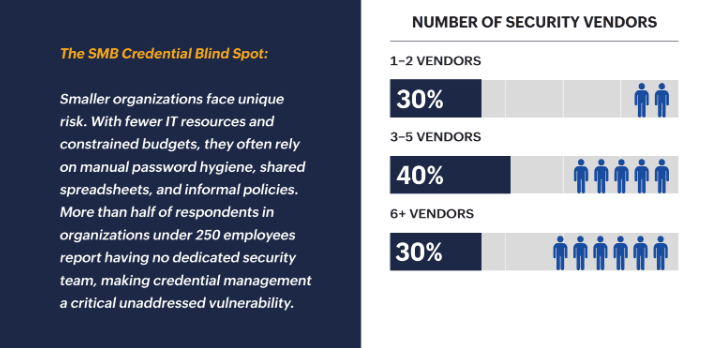
Small businesses in particular will face risks related to password credential security both now and in the coming years.
More than 50% of businesses with 250 employees or fewer don’t even have a dedicated security team, the survey says. This forces them to rely upon informal security policies.
Imagine depending on your already busy employees to implement regular password updates, for example.
But making the changes necessary to protect your businesses may not be optional. Your company’s very survival may depend upon it.
Survey Highlights How U.S, Companies Face Greater Risk Despite Spending
And again, businesses around the world from China to the Middle East face many of the same challenges when it comes to password credential security.
But for U.S. businesses, the problem seems worse despite the fact that these companies budget consistently higher for security.
The thesis these numbers suggest seems obvious. Budget matters less when protecting your business from cyberattacks than software architecture.
Better Software Architecture Offers Greater Security
“The organizations that will navigate the next five years most effectively are those investing in architectural simplicity, building governance models that scale with identity growth, and adopting AI-enabled orchestration to reduce friction,” says Helen Yu, founder and CEO of Tigon Advisory Corp.
Fortunately for all businesses but especially those SMBs, you can take steps to future proof your security without big expenditures.
“Budget is not the primary constraint on security maturity; architecture, talent, and visibility infrastructure are. The data in this report is a call to sequence correctly: fix foundations before chasing advanced capabilities,” Yu adds.
To learn more about how software architecture helps shield your small business from devastating cyberattacks, contact Zoho today.
The Digital Landscape Contains Many Threats
The digital landscape has become a minefield. You may run a tour guide service in Nantucket, Massachusetts, or a fintech company in Burlington, Vermont.
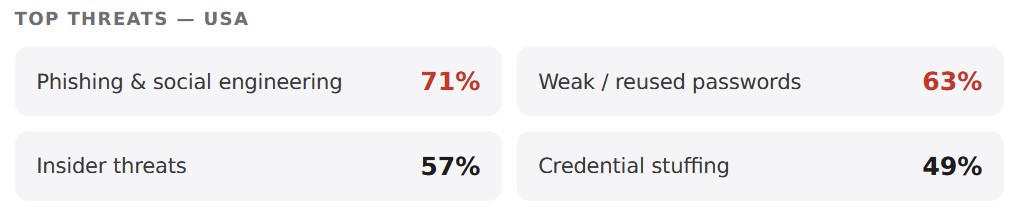
The threats to your business remain the same. Here are some of the top ranked risks according to survey responders from businesses just like yours.
Phishing
Phishing or some other kind of social engineering ploy topped the list of threats with 71% of U.S. respondents.
A classic version of this attack involves a deceptive email sent to one of your employees. Perhaps this email appears to originate from a customer or supplier.
But once your employee clicks on an innocent looking link inside the email, you’re hooked like a flounder.
The link allows the sender to steal sensitive information, distribute malware or gain unauthorized access to your system.
Weak Passwords
We’re all guilty of this one. Nonetheless, 63% of U.S. respondents listed this as a major threat in the survey.
Say your employees need to log into 15 or more apps during the course of their day as we’ve determined many do. They need a different password for each.
But instead of picking a hard to guess password with letters, numbers and other symbols, they choose the first 12 letters of the alphabet.
Then to make matters worse, they use the same password for all 15 apps so guessing one gives a cyberattacker access to them all.
Inside Threats
Sure, you like to trust all your people. And you want to believe none of them would do anything to intentionally jeopardize your business.
But an unscrupulous employee with access to your payment portal or online bank accounts or a subcontractor with access to sensitive client information could certainly spell trouble.
It seems a threat from the inside keeps at least 57% or U.S. survey responders up at night.
Credential Stuffing
This attack further amplifies the danger of weak or reused passwords.
Though even businesses with strong passwords for each individual app could find themselves vulnerable if these passwords aren’t routinely updated.
The scenario goes something like this. An attacker buys a list of passwords from a data breach, then uses a bot to stuff these passwords into multiple apps until access is gained.
If your employees have carelessly failed to update their passwords or have reused them for multiple apps, an attacker could quickly gain complete control of your business.
According to the survey, 49% of U.S. respondents worry about this threat regularly.
Third Party Access
Finally, 41% of business respondents to the survey worldwide fret about unmanaged third party access.
Think of this as the digital equivalent of giving contractors or other non-employees unsupervised 24-hour access to your business office or other facilities.
Suppose you run a massive website with hundreds of freelancers including content creators, designers, SEO consultants and web developers.
Giving them access to your site so that they can load content, change banners and logos, optimize pages and update code makes sense. Otherwise you need to do all this work yourself.
But giving hundreds of contractors unlimited and unmanaged access to your website may lead to trouble.
Unscrupulous contractors might insert unwanted content, steal digital assets, sabotage SEO to benefit other clients or maliciously destroy website functionality.
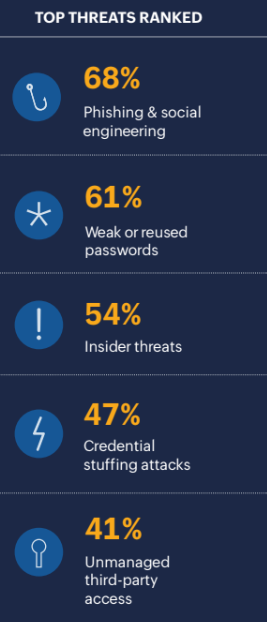
Threats Ranked Globally
AI Provides A Better Option for Password Credential Security
Most respondents to the Tigon survey agree AI holds the key to better security. However, almost no businesses seem ready to implement it.
AI provides a more robust protection against cyberattacks and delivers better password credential security.
It does so in a variety of ways and offers an attractive option for small businesses who lack a dedicated security team.
Here’s what the survey reveals about preferred AI security features amongst respondents world wide.
Anomaly and Threat Detection
A reported 68% of respondents indicated a preference for anomaly and threat detection.
AI alerts your team of unauthorized access to sensitive files. Perhaps you manage a physician’s office and need a way to detect suspicious attempts to access patient records, for example.
Or perhaps the credentials of one of your team based in the U.S. is suddenly used to attempt access to your system from somewhere in Eastern Europe or South Asia.
AI uses machine learning to detect unusual activities that might constitute a threat to your business and stops them in their tracks.
Automated Policy Enforcement
Another 61% of survey respondents favored automated policy enforcement as a preferred AI security feature.
You may recall one of the greatest challenges facing small businesses lacking a dedicated security team.
Employees need to rely on their own informal security policies. This would include things like remembering to update passwords and trying not to use weak or reused passwords.
With AI, much of this can be automated leaving employees to focus on more high level tasks without interruption.
AI can even detect when a user attempts to update a password by using a breached credential and blocks their access immediately.
Behavioral Analysis
An additional 54% of survey respondents believe behavioral analysis might be most helpful in neutralizing threats to your password credential security.
AI can go the extra mile to secure your company’s logins. Again, using machine learning it establishes behavioral baselines.
Then it springs into action if it detects activities deviating too far from those baselines – even if a user has the correct password.
Suspicious logins by an employee at 4 a.m. on Sunday when they generally work 10 to 6 weekdays might raise a red flag, for example.
Risk Based Access Control
Finally, 47% of respondents worldwide indicated a preference for risk based access control.
This AI security feature assigns risk scores to unusual actions like attempts to login from a previously unknown device.
The AI then requires additional authentication from the user assuring against unauthorized access.
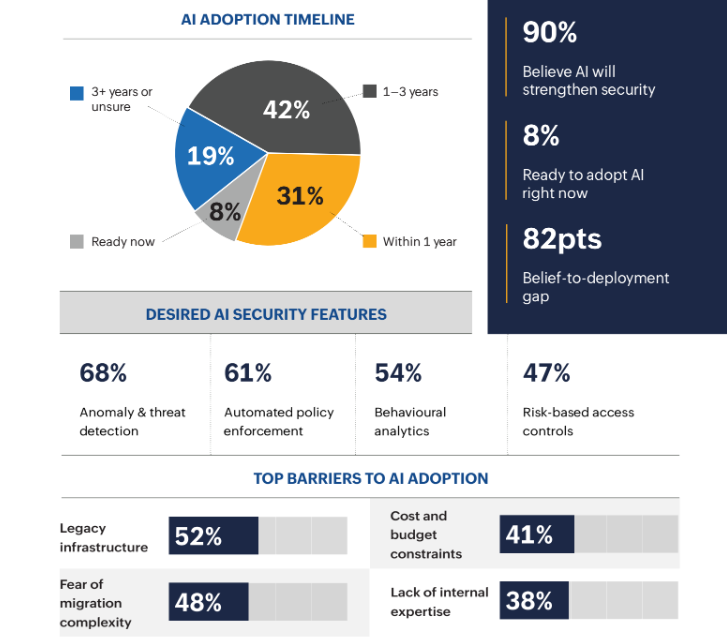
U.S. Businesses Show Widest Gap Between Awareness and Implementation
Whether you own a bakery in Des Moines, Iowa, or a PR firm in Peoria, Illinois, implementing AI security would put you at the head of the pack.
While 91% of U.S. business respondents understand the importance of AI to their security, just 9% are ready to integrate AI security into their operations.
This 82% AI gap between awareness and integration is wider than for businesses in any other region in the survey.
What’s more, many U.S. businesses are far from ready to implement AI security for logins, the survey says.
With password security still being managed by shared spreadsheets and browser saves, U.S. businesses must be prepared for big changes before adopting AI password security.
In Conclusion
You may operate a pick and pack plant in Tamaqua, Pennsylvania. Or you may manage a light manufacturing company in St. Paul, Minnesota.
Even in these businesses where employees traditionally work onsite, hybrid and remote roles are emerging.
These hybrid and remote workers may perform logistics planning, data entry or inventory management tasks using a variety of software and with multiple logins.
As discussed earlier, this multiple login environment combined with application sprawl creates greater risk to password credential security.
This makes your business ever more vulnerable to an invisible army of cyberattackers scattered across the internet and around the world.
But don’t panic! Future proof your security stacks with solutions that safeguard your business today and tomorrow. Contact the Zoho Sales team today.
Images via Zoho

![[Aggregator] Downloaded image for imported item #1399495](https://www.sme-insights.co.uk/wp-content/uploads/2026/05/Zoho-Survey-Warns-of-Huge-Password-Security-Threat-v1.jpg)